Cloud 2.0: Securing Trust to Survive the ‘One-In-Five’ CSP Shake-Out
The Cloud market is on the verge of the next wave of market penetration, yet it’s likely that only one in five Cloud Service Providers (CSPs) in today’s marketplace will still be around by 2018, as providers fail or are swallowed up by aggressive competitors. So what do CSPs need to do to survive and prosper? (October 2013, Foundation 2.0, Executive Briefing Service, Cloud & Enterprise ICT Stream.)
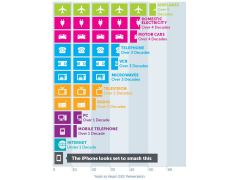
Technology adoption rates Sept 2013
